Industry Solutions
Manufacturing Industry
THE MANUFACTURING INDUSTRY FACES MANY THREATS
Manufacturing is currently undergoing incredible change. Smart Manufacturing and Industry 4.0 mean more connected devices than ever before. There are clear benefits to this, but it also creates more vulnerabilities in your network. Vulnerabilities that state sponsored threat actors and cybercriminals will exploit to access your priceless intellectual property. Clearnetwork USM’s unified approach means greater security efficiency so advanced network monitoring doesn’t break the bank.
Common cyber security challenges facing the manufacturing industry:
- Protect sensitive data, capital and intellectual property
- Defend against operational disruption and industrial espionage
- Reverse an industry-wide lack of security awareness
- Mitigate supply chain cyber risk
- Manage security in the Industrial Internet of Things era
- Eliminate vulnerabilities in Industrial Control Systems
Key security questions manufacturers must ask
Security questions manufacturers should be asking of their cyber security:
- How are we managing security risks in the supply chain?
- Are Industrial Control Systems tested for vulnerabilities? How often?
- Are systems in place that can defend against sophisticated threats?
- Are systems able to detect threats that have passed the perimeter?
- Is there a plan in place to identify, respond to, and report breaches?
- What systems/controls are used to mitigate insider threats?
- What is being done to manage supply chain security risks?
CLEARNETWORK DELIVERS COMPREHENSIVE MANGED SECURITY SERVICES
Clearnetwork’s USM platform provides a unified approach to threat detection and compliance management that provides complete IT security visibility. USM is an all-in-one security management platform that includes five essential security capabilities all centrally managed through a single pane of glass:
Asset Discovery
Vulnerability Assessment
Intrusion Detection
Behavioral Analysis
SIEM/Log Management
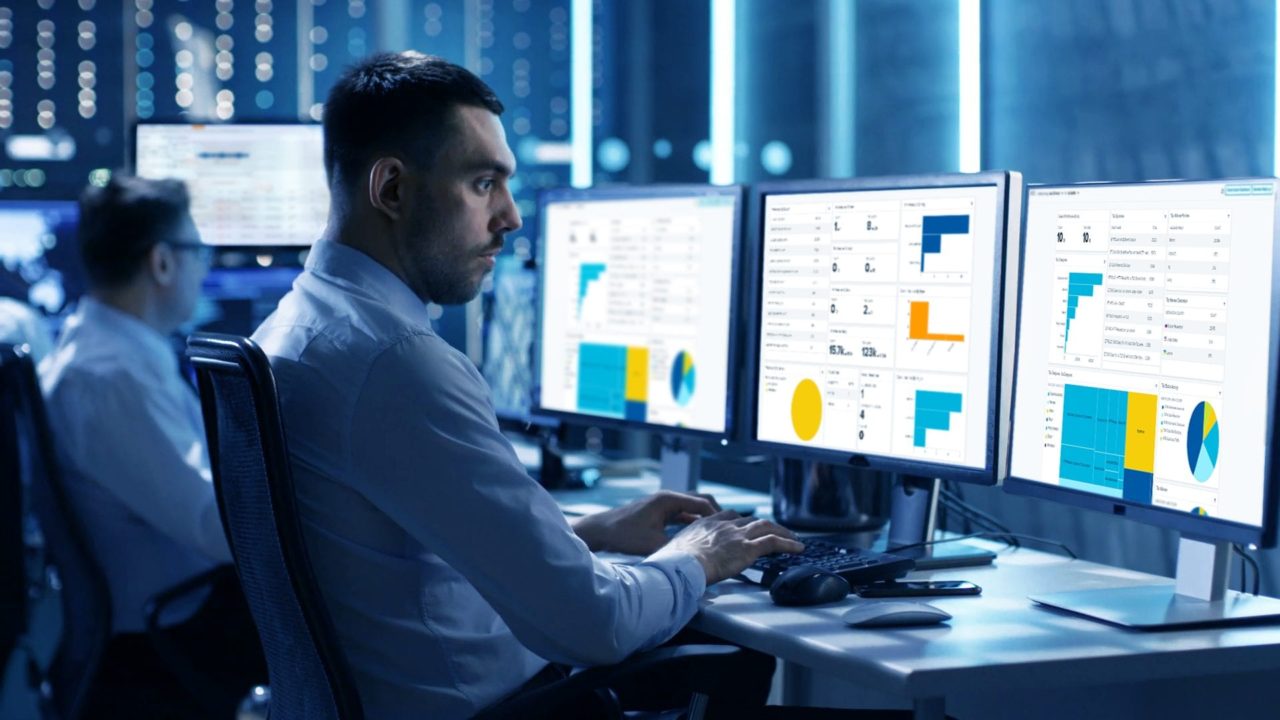
MAINTAIN VISIBILITY OF YOUR ONLINE ASSETS AND RESPOND QUICKLY TO THREATS
We are a managed service that allows your firm to concentrate on value-added functions and business processes rather than performing labor-intensive security tasks. Our customers experience peace of mind knowing their data is safe and that their networks, cloud environments, and endpoints are being monitored.
Experienced Team
Our analysts have experience monitoring networks like yours and understand the unique security needs of the manufacturing industry.
Rapid Deployment
It’s quick and easy to get started. Customers typically set up USM in under an hour and one of our experts will be there to help you every step of the way.
Unrivaled Support
Don’t spend hours waiting for a response to your ticket. Our support team will get back to you in minutes and work with you for as long as you need us.