A Leading MSSP for SMBs
Our US-based security experts help SMBs defend against cyber attacks,
and meet compliance with managed security services.
SOC as a Service (SOCaaS) | Managed Alienvault | Managed CrowdStrike EDR |

98%
CUSTOMER RENEWAL RATE
200+ Customers
IN A VARIETY OF INDUSTRIES
100%
CYBERSECURITY FOCUSED
At Clearnetwork, we defend your Infrastructure like it’s our own
Clearnetwork’s US-based team of cyber experts are here to help with a wide variety of expertise to reduce cyber risk, achieve and maintain compliance, and reduce the workload on your resource constrained IT team, all cost effectively.
CHALLENGES
Let us solve your cyber security challenges
From managed services to consulting, our team is ready to help
Managed SOC Services To Protect Your Infrastructure
Maintaining Security with a Remote Workforce
Achieving and maintaining Compliance
Internal & External penetration testing
Minimizing the threat from ransomware
TESTIMONIALS
What our clients say about us
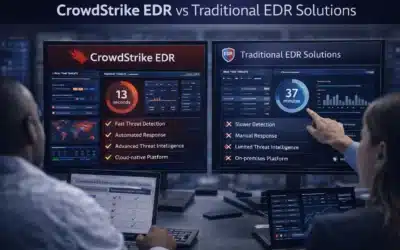
CrowdStrike EDR vs Traditional EDR Solutions: A Comprehensive Comparison
Not all EDR platforms are built the same, and the gap between CrowdStrike EDR and traditional endpoint detection tools has widened considerably as attack...
What to Expect from Leading EDR Solution Providers in 2026
The expectations organizations bring to EDR solution providers have shifted considerably. A few years ago, behavioral detection and automated response were...
The Future of Network Security Monitoring: Trends and Innovations for 2026
The way organizations monitor their networks has changed more in the past three years than in the previous decade. Hybrid infrastructure, cloud-native workloads,...