Why Managed Detection Response is Important
Review the 10 reasons why managed detection response services may be the most effective way to keep your network safe from hackers.
Can your team manage these ten examples of danger to your network effectively?
1. Users will always download harmful content, either wittingly or unwittingly.
Hackers know that if a user can surf the web freely and download content, they also have the ability to execute the hacker’s own code that will compromise the user’s system and give the hacker access to the corporate network. So, hackers use the lure of “special content” to get unsuspecting users to click on links to their programs. CLEARNETWORK: MDR detects users’ attempts to access such content (whether real or fake), as well as the immediate consequences of the malicious download so that you can take immediate, specific action.
2. Your current IT staff cannot devote the necessary time to look at logs from servers and firewalls. Our MDR Team is Focused on Your Security.
Over-taxed IT departments do not have the time to review logs from network devices and servers. Because of this, security and configuration-related problems go on for days and weeks without being resolved, leaving the door open for malicious users or hackers to compromise systems and corporate data. CLEARNETWORK: MDR sensors alleviate much of the need to perform this function internally, as they can see network activity outside of the devices and hosts, and our engineers can alert you to important events.
3. It would take a team of a full-time security professional to do Network Monitoring correctly. Our team is fully Trained for managed detection response.
Managed Detection and Response is a labor-intensive process, and requires a high level of expertise with networking protocols such as Ethernet, IP, TCP, and upper-layer protocols such as FTP, HTTP, etc. Network Administrators are usually not trained to forensically investigate intrusion attempts, or to distinguish between malicious traffic and a normal ‘chatty’ application. CLEARNETWORK security engineers bring a trained and experienced eye to the process so that your organization receives timely actionable intelligence with which to respond quickly and decisively.
4. The risks of not knowing have become too great for a business NOT to monitor the network.
It has become a trivial matter for someone to download a hacking program, and use it against your network. Whether the tool is OpenVAS, mpak, or the myriad other utilities out there, someone with very little knowledge can do a great deal of harm. You need to know if someone is fooling around on YOUR network, or is on the outside targeting your network. CLEARNETWORK: MDR gives you the visibility to do that in the most cost-effective way.
5. Computers will never be totally secure but Using MDR services will minimize your risk
Internet browsers, Java and Flash Player are tools that are essential for getting work done, but they are full of vulnerabilities, known and unknown, that can allow an outsider to gain control of your user’s desktops and the information contained on your networks. CLEARNETWORK: MDR quickly alerts you when a user attempts to access malicious content.
6. You want a security infrastructure that supports tomorrow’s networks as well as today’s. A MDR Service will help.
CLEARNETWORK: MDR is flexible and is not restricted to any detection approach and does not solely rely on traditional signatures. CLEARNETWORK: MDR can also be easily expanded to fit your growing organizational needs.
7. You need to know when someone has compromised your web-based applications and databases.
Most web applications utilize back-end databases. If an application has not been written to protect against invalid database queries, hackers can use your own web forms to gain administrative access to your database server, its information, and then the entire network it resides on. CLEARNETWORK: MDR detects when such an attack attempt occurs and helps you prevent catastrophic harm to your business.
8. You utilize web-based applications from third parties.
Many applications that are delivered over the web utilize technology that requires advanced permissions on a given workstation. Your PC warns you when you access one of these applications, but users often click “OK” without thinking, and give these applications all the permission they need to take full control of a computer. When this happens, a malicious application will typically use network resources to either traMDRit information about your network, or download instructions from the hacker’s command-and-control infrastructure. CLEARNETWORK: MDR gives you the visibility you need to discover when a malicious application is using your network, so you can take immediate steps to remove it.
9. You don’t apply vendor-supplied patches on the day they are released.
Desktops are a major target. Users run all kinds of vulnerable software. Most notably, Java and Flash Player. The truly concerning fact about desktop software is that most vendors give us no tools to manage an enterprise environment. This means we are relying on our users to click OK when a software update notification pops up. We have told them for the past 20 years to click cancel if you are not sure what you are about to do. A good managed detection response team can help monitor and ensure that patches are done correctly.
10. You don’t know what Managed Detection and Response truly is or why you need it.
Need more explanation? No problem. Give us a call at (800) 463-7920 x3, and we’ll be glad to discuss your current security posture, and how we can help you sleep better at night.
LEARN MORE ABOUT MANAGED DETECTION AND RESPONSE IN OUR BLOG
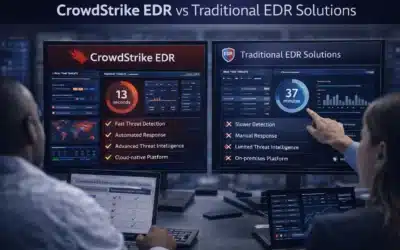
CrowdStrike EDR vs Traditional EDR Solutions: A Comprehensive Comparison
Not all EDR platforms are built the same, and the gap between CrowdStrike EDR and traditional endpoint detection tools has widened considerably as attack techniques have grown more sophisticated. Understanding what that gap actually consists of — beyond marketing...
What to Expect from Leading EDR Solution Providers in 2026
The expectations organizations bring to EDR solution providers have shifted considerably. A few years ago, behavioral detection and automated response were differentiators. In 2026, they are the baseline. What separates strong providers from the rest has moved up the...
SIEM Solutions Comparison: Key Features and Benefits of Leading Platforms
Any meaningful SIEM solutions comparison has to go beyond spec sheets. Feature parity across major platforms has grown significantly — most enterprise-grade tools now check the same foundational boxes. What actually separates them is detection architecture, pricing...